Malware "Big Brother" films what you do in VR

A new malware can record the screen of a VR headset and send the footage back to the attacker, according to New York-based cybersecurity firm Reason labs, which identified the threat.
How does the "Big Brother" malware work? And how can you protect yourself?
According to Reason labs, the malware originates from a PC malware program installed and executed on a Windows computer. The malware then lies dormant on the system until an Android-based VR headset with developer mode enabled connects to the PC. Possible candidates include the Meta Quest 2 (review), the Pico Neo 3 Link (review), and the Vive Focus 3 (review).
The VR scene is filmed and sent out
The malware opens a TCP port that allows attackers to record and save VR sessions on the PC. One prerequisite is that the VR headset is connected to the same WLAN as the PC - a cable connection is not required. The TCP port then transmits the recorded material to the attacker - for industrial espionage or blackmail, in the case of compromising material.
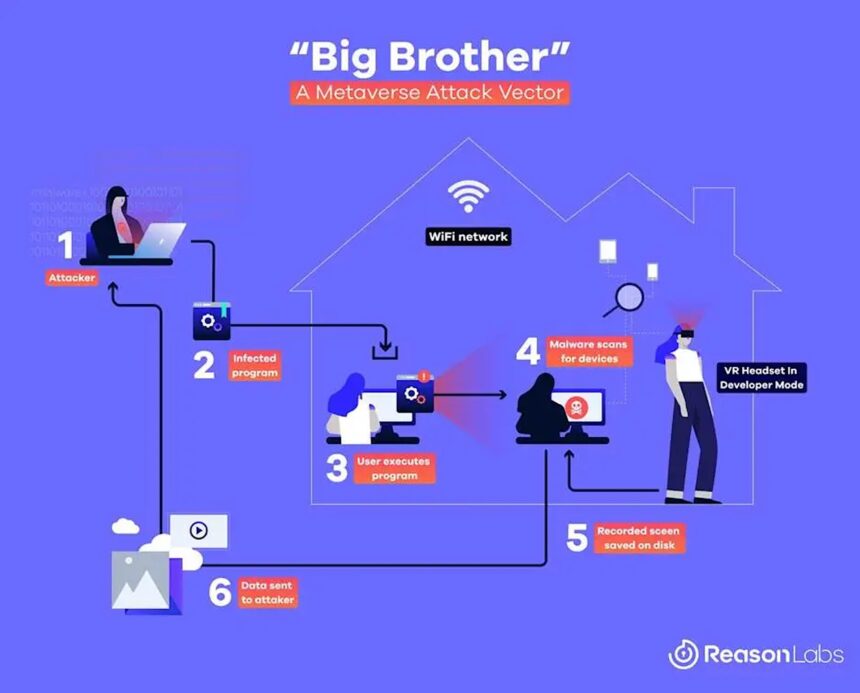
This is how the malware attack works. | Image: ReasonLabs
At risk are companies, developers, and VR enthusiasts who use both PC VR streaming and sideloading. Sideloading requires that you enable developer mode. It can be particularly dangerous when working on the PC via VR headset and accessing sensitive information or entering passwords.
How to prevent an attack by "Big Brother
The fact that something like this emerged should not surprise anyone. The proliferation of such devices is increasing and with it the attractiveness of developing virtual reality-specific malware.
Over time, malware is likely to emerge that attacks VR headsets without going through a PC. VR web browsers are a particularly vulnerable interface. It would be easy to catch malware on an infected website, provided Android has a corresponding security hole. Meta, HTC and Pico have not yet commented on the Big Brother malware.
To be on the safe side, only activate the developer mode during sideloading or check whether the desired VR app is also available in the App Lab. Meta's alternative app store does not require sideloading.
Note: Links to online stores in articles can be so-called affiliate links. If you buy through this link, MIXED receives a commission from the provider. For you the price does not change.